- Published on
CWL - Who Am IAM?
- Authors

- Name
- mfkrypt
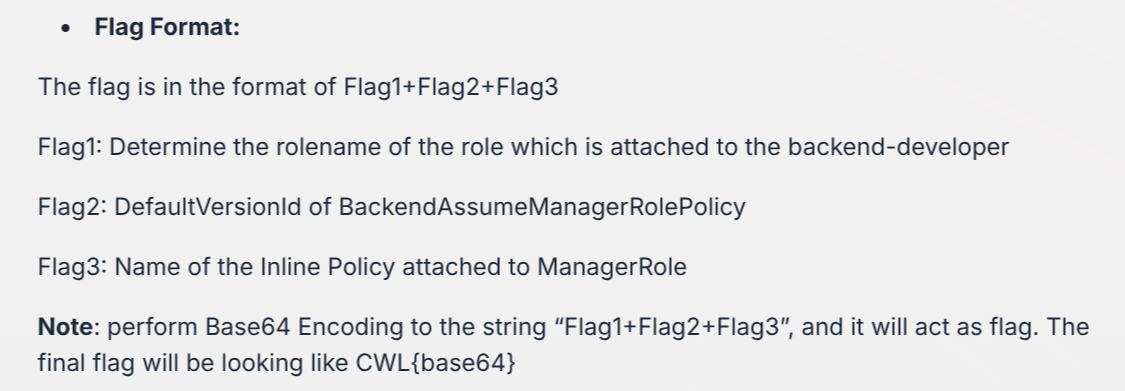
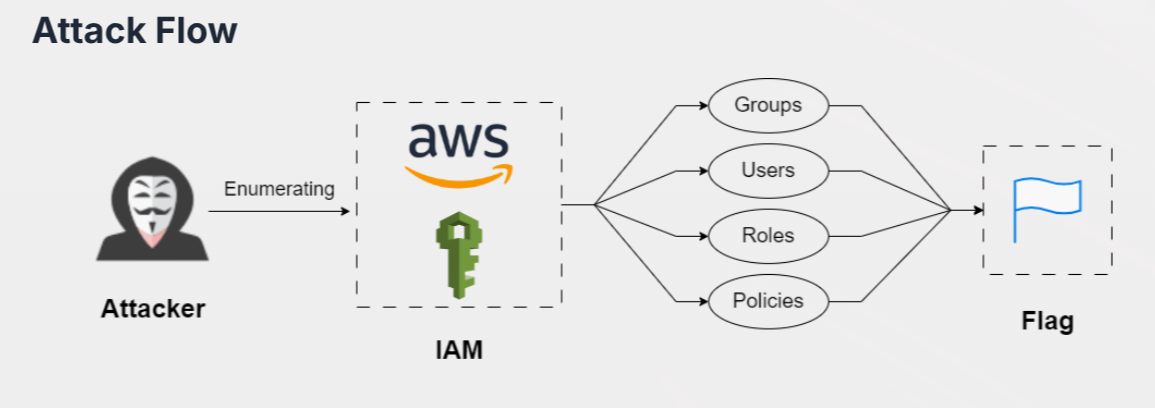
Table of Contents
Recon
We are given the following credentials:
Proceed to authenticate. Just provide any random region and we can leave out the output format field
aws configure
Verify the authentication by making an API call
aws sts get-caller-identity
Our current user is frontend-developer
1'st Flag
Roles Enumeration
The first task is to find the role that is attached to the backend-developer user. Originally, the awscli tool does not provide the functionality to search for specific users for attached roles. Instead, the command that comes close to this lists all the roles available which is a lot of information to go through. So, we improvise by using this command which lists all roles and filters (via jq tool) for role name and associated users
aws iam list-roles --output=json | jq '.Roles[] | {role: .RoleName, user: .AssumeRolePolicyDocument.Statement[].Principal.AWS} | select(.user != null)'
2'nd Flag
Policy Enumeration
The second task is to acquire the Version ID of BackendAssumeManagerRolePolicy policy. To do this we need to retrieve the ARN of the said policy.
aws iam list-attached-user-policies --user-name backend-developer
{
"AttachedPolicies": [
{
"PolicyName": "BackendS3ReadOnlyPolicy",
"PolicyArn": "arn:aws:iam::058264439561:policy/BackendS3ReadOnlyPolicy"
},
{
"PolicyName": "BackendAssumeManagerRolePolicy",
"PolicyArn": "arn:aws:iam::058264439561:policy/BackendAssumeManagerRolePolicy"
}
]
}
Now retrieve the Version ID
aws iam get-policy --policy-arn arn:aws:iam::058264439561:policy/BackendAssumeManagerRolePolicy
3'rd Flag
Inline Policy Enumeration
The third task is to identify the name of the Inline Policy for the discovered role, ManagerRole. Inline policies differ from normal policies (managed policy) by being embedded into a single IAM identity such as a user or a role.
aws iam list-role-policies --role-name ManagerRole
{
"PolicyNames": [
"ManagerRole-inline-policy"
]
}
Combined Flag
Plaintext flag before Base64 encoding
ManagerRole+v1+ManagerRole-inline-policy
Base64 flag
CWL{TWFuYWdlclJvbGUrdjErTWFuYWdlclJvbGUtaW5saW5lLXBvbGljeQ==}